I will reverse engineer your binary, protocol, or compiled code
Reverse engineering reality
About this Gig
I reverse engineer compiled software when source code and documentation are unavailable.
I work directly with stripped binaries, undocumented protocols, embedded firmware, and IPC mechanisms where traditional analysis fails.
WHAT I CAN ANALYZE
Native executables (x86, x64, ARM)
Stripped binaries with no symbols
Undocumented network protocols
Proprietary file formats
IPC mechanisms (D-Bus, Unix sockets, custom)
Serialization formats (protobuf, Capn Proto, custom)
Embedded Linux firmware
WHAT YOU GET
Clear documentation of program behavior
Reconstructed data structures and protocols
Code flow and execution paths
A technical report you can actually use
REAL EXPERIENCE
I specialize in cases where documentation is missing, vendors are unresponsive, or original developers are gone. Recent work includes reconstructing Capn Proto IPC protocols, proprietary XML schemas, and custom binary formats from stripped binaries.
USE CASES
Lost source recovery, legacy documentation, security assessment, protocol interoperability, malware triage.
NOT OFFERED
Cracking, piracy, license bypassing, or anything illegal.
Message me with what you need analyzed and Ill tell you if its feasible.
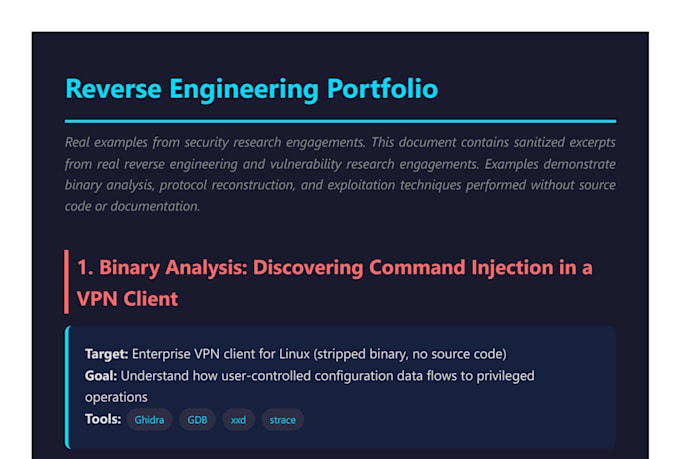
My Portfolio
FAQ
What information do you need to get started?
At minimum, I need the binary or firmware image and a clear description of what you want to understand or achieve. If you have sample data, logs, network captures, or observed behavior, that helps, but it’s not required.
Do you need source code or documentation?
No. My work is specifically focused on situations where source code and documentation are missing, incomplete, or unavailable. I work directly with compiled binaries and runtime behavior.
Can you guarantee a vulnerability or exploit?
No. Reverse engineering is investigative work. I guarantee a thorough, professional analysis and clear documentation of findings, but not the existence of a specific vulnerability.
Is this service legal and ethical?
Yes. I do not perform piracy, license bypassing, DRM cracking, or illegal activity. Work must be lawful and within ethical or contractual boundaries.
What does the final delivery look like?
You receive a written technical report explaining behavior, data structures, execution flow, and relevant findings. This may include diagrams, pseudocode, and recommendations depending on the project.
Do you sign NDAs or handle sensitive material?
Yes. I regularly work with confidential binaries and private systems and am comfortable signing NDAs if required.
How long does a typical analysis take?
It depends on size and complexity. Small binaries may take a few days, while firmware or protocol-heavy projects can take longer. I’ll give a realistic estimate before starting.